Is WinZip Driver Updater a Virus and How Do You Remove It in 2022
If you want to install Discord on your PC, however, simply head to discord. Video showing how to start Windows 8 in “Safe Mode with Networking”. Click and stretch the top edge upwards with the mouse to make the menu taller. It can split files to download into sections, and download each section simultaneously. This item locate in folder “System32”. STEP 3 Now scroll down to the option that states: Configure shield settings and head towards the Mail Shield tab beside Web Shield. Logitech Options is extremely easy to use yet it provides amazing features. The BSD approach is more conservative, taking into account the fact that filesystem inconsistencies do on occasion crop up at times other than system crashes. It should be simply excluded from the results as it makes no sense there. This will perform another analysis, which can take a few minutes, especially if it detects those Windows Update backup files that we mentioned earlier. However, it has been discovered that the Win32 Malware gen variety is a particularly dangerous type of malware when it comes to the security of your personal credit card details, account passwords, crucial data, and other financial data. It features smart volume reduction that https://parsons-technology.com/what-is-a-video-accelerator/ dynamically adapts to your media content. Store at room temperature away from moisture and heat. Here is a method in few easy steps that should be able to uninstall most programs.
Download and Manage Files Nicely Securely Freely
BiometricYubiKey Bio Series supports biometric authentication using fingerprint recognition. When considering complaint information, please take into account the company’s size and volume of transactions, and understand that the nature of complaints and a firm’s responses to them are often more important than the number of complaints. Family Vacation 2: Road Trip HKLM x32. Your computer will appear to do nothing. While you may be able to get a free trial of TruthFinder and make a free phone number lookup, usually you need to pay a monthly membership fee. MovieStarPlanet games, websites, etc. Today, Adobe Photoshop is used by a wide range of designers and creative practitioners in the field. View: 44138 • Category: Home » bluetooth » Atheros. You can connect with them anytime from Monday to Friday between 10:00 AM to 8:00 PM EST. During her college days, she also developed a passion for computer related stuff which lead her to become a technical writer indeed. All of the immortals loathed him, with three notable exceptions. “Nikon Message Center 2″=”c:program files x86NikonNikon Message Center 2NkMC2. A common use of netsh is to reset the TCP/IP stack to default, known good parameters, a task that in Windows 98 required reinstallation of the TCP/IP adapter.

Contact
Fill in your details below or click an icon to log in. However, our keyboard cannot read or access anything on your iPhone or anything you type using your iPhone keyboard or any other third party keyboards. We’re seeing more and more antivirus products adding modules specifically designed for ransomware protection. Additionally, ASTincreased by 10 fold and the hepatobiliary liver injury marker,bilirubin, increased by 1. Encryption and decryption are handled seamlessly, so you don’t have to modify your applications to access your data. 15 Days Trial +Includes DocuBay and TimesPrime Membership. From running memory checking software to scanning for viruses, these are processes that can take some time. With Windows 10 Home > I maybe did not find options to disable entire “App and Browser Control” under Windows Defender Security Center. As well I did have it set to ‘remeber me’ but my password was gone so I had to re enter it but I know my password so why won’t it let me on. This was one of the Top Download Picks of The Washington Post and PC World. The prefix in changes its form to il before an l; to im before b, m or p; and to ir before r. Many businesses, especially those operating a web server, are “all systems go” all the time. For complete removal of K9 Web Protection, you can manually detect and clean out all components associated with this application. Project and Task Management. IN THE EVENT ANY CLAIM RELATING TO THE PERFORMANCE OR NONPERFORMANCE BY MOVIESTARPLANET GROUP OF GAMES PURSUANT TO THESE TERMS AND CONDITIONS, OR IN ANY OTHER WAY CONCERNING THE MOVIESTARPLANET GROUP OF GAMES WEBSITES, IS MADE BY YOU, THE ACTUAL DAMAGES TO WHICH YOU MAY BE ENTITLED SHALL BE LIMITED TO THE FEES, IF ANY, PAID BY YOU FOR USE OF THE MOVIESTARPLANET GROUP OF GAMES WEBSITES. I decided to research this further. Otherwise the BIOSmay use these resources for some other device and create conflicts. HTML: This is the primary language that web browsers understand. I’ll start from scratch, then progress through detailed examples of cherry picked settings to arrive at an excellent, post processed archive. Check the “Yes, this is a game” checkbox to load the Game Bar. Step 8 A pop up window will appear. Then you’ll open Realktek HD audio manager. Image credit: Ascannio / Shutterstock. App uploaded by: Nor de Ana. There’s no reason to get alarmed by this unless you notice that your CPU is overheating. Click Start to open the Start menu, click the Power button, and click “Restart” while holding the Shift key on the keyboard. It is designed to detect and correct inconsistencies between them, such as disk blocks marked as in use that are not claimed by any file, and files existing on disk that are not contained in any directory. Nowadays, using a strong password for your online accounts is very important. Scan the QR code to download App. It means a benign program is wrongfully flagged as malicious due to an overly broad detection signature or algorithm used in an antivirus program.

How to Take Macro Photos on iPhone 13 Pro and iPhone 13 Pro Max
You may unsubscribe from these communications at any time. Select PC Accelerate Pro or any suspicious items and then Click on Uninstall button to remove it from Windows. ArtPlus File Shredder is one of the simplest file shredding software in this list, that is capable of shredding files only. In order to access your ATT. The free version of this audio enhancer comes with many limitations discussed below, but provides necessary tools to enhance music/audio including equalizer and many sound Effects. Users require no additional hardware to run it, and they can directly cast their iPhone or Mac to their Smart TV. If the issue is with your Computer or a Laptop you should try using Restoro which can scan the repositories and replace corrupt and missing files. From the Mozilla Firefox settings tab, choose the Troubleshooting information option. Please don’t put logs in code or quotes. You can use Group Policy or whatever 3rd party software distribution service you prefer to deploy the agent in your network. Homer does not detail the outcome of this story but it is generally believed that the marriage gifts were never repaid to Hephaestus, for Ares decided if Zeus was not obligated to pay than neither was he. Echo this command is default system32 directory for x86 OS or x64 OS. So without further ado, let’s check them out.

Other Process:
The image below shows that the Desktop Window Manager is the biggest user of memory on the Windows 11 computer. Retrieved information about cloud service from. 75 MBHow to install: sudo apt install ruby svn. You may hear the term ip address as it relates to online activity. Storage Sense is a feature built into Windows that can help free up space automatically by removing files you no longer need. Moreover, a handful of people have been victims of the Edgar cut meme and have still not recovered from the damage. Thus, the most important thing you must do, if possible, is to back up the disk data before you start to reimage computer. Following exploitation with LOWBALL malware, admin@338 actors created a file containing a list of commands to be executed on the compromised computer. A potentially unwanted program PUP or potentially unwanted application PUA is software that a user may perceive as unwanted or unnecessary. The YubiKey 5 Series models can be more than twice the price of the Yubico Security Keys, but their robust compatibility with more devices and accounts makes them worth the higher price. Exe” which doesn’t appear in either under normal conditions but does via CTRL+ALT+DEL. Delete Diagnostic Data collected by DiagTrack or Connected User Experience and Telemetry: Press Windows Key + S and type ‘privacy’ in the search box. Currently, you have to download the ADMX templates for all browsers except Internet Explorer and save them in the central store or the local workstation. Check out this post which is one of the most popular of all time. Process Explorer is considered to be a more advanced form of the Windows Task Manager. These include operating system, CPU, RAM, motherboard, optical drives and audio. As it is a Windows program, thus to install it on Linux, we have only one option that is using Wine HQ, thus we won’t give any guarantee that it will work perfectly on your system, however, give it a shot just because it worked fine in our case. 22222222 Pin: 4754: If you are looking for a Filelinked store with the latest CyberFlix, Terrarium TV, Cinema APK, Morph TV, MX Player, Mouse Toggle, Cloud TV, Titanium TV, Kodi APK, IPVanish, Aptoid TV, Redbox TV, Live Net TV, BeeTV, Magic TV, Morpheus TV, TVZion, Nord VPN then is time to try this store code. Privacy practices may vary, for example, based on the features you use or your age. Note: We will not share your personal data with any third parties. In this post, I will show you the easiest way to activate the front panel audio jack in Realtek HD Audio Manager. Write a review for Logitech Options. Total ALT in the plasma increased by 4 foldfrom 18 U/l before the race to 72 U/l after the completion of therace Table IV. The third one has old registration data from Emsisoft Anti Malware that could be removed. Gen using Control Panel. “This term is often used on social media or in text messaging. Uninstall from largest to smallest. This was one of the Top Download Picks of The Washington Post and PC World.

DAEMON Tools Lite related software
If driver support is legit how did it get on my computer without my consent. Unplug the controller from your Mac. The HP SimplePass software is the fingerprint reader. By following this guide, you will be able to uninstall and therefore disable OneDrive for everyone on your PC. Outlook provides a template for creating these events, called Rules and Alerts. By default all programs are set to update automatically, so why hasn’t this program updated within the 45 days it claims it will execute automatically. You can browse the location of your clips and load one of them unless it is formatted as AVI, MKV, WebM, MP4, FLV, or MPEG. To impress the hiring manager, research the job duties and responsibilities, the company, and its products and services. NET Framework, InstallShield, and Conexant use the basic name. Key features included. Mann, considered one of the world’s most influential climate scientists, will speak in Bend on March 31 about the urgent need to reverse decades of climate inaction and prevent the worst impacts of a climate crisis. The incident was discovered and reported by Talos. You must have listened to a lot of rap battles in the past but none can compare to the epic contest for AI dominance between Amazon’s Alexa, Apple’s Siri, Google’s Assistant and Samsung’s Bixby. Skype changes the way people stay connected virtually, and it even simplifies things while providing many of the important features that Discord provides. On the left is what my Flickr photo stream looks like to me, and on the right is what it looks like to others. Just how much does it cost to download. So one drive in your PC is usually for games and the other is probably for Windows and other documents. Exe /frequentupdate SCHEDULEDTASK displaylevel=FalseThis task ensures that your Microsoft Office installation can check for updates. Watershed Defense Fund. Unfortunately, virus scan results and additional ads that come from the app are not necessarily trustworthy. If you notice that Runtime Broker is consistently consuming 30% or more of your CPU, showing higher than expected memory usage, or spiking the usage even when you don’t have a universal app running, there are a couple of potential explanations.

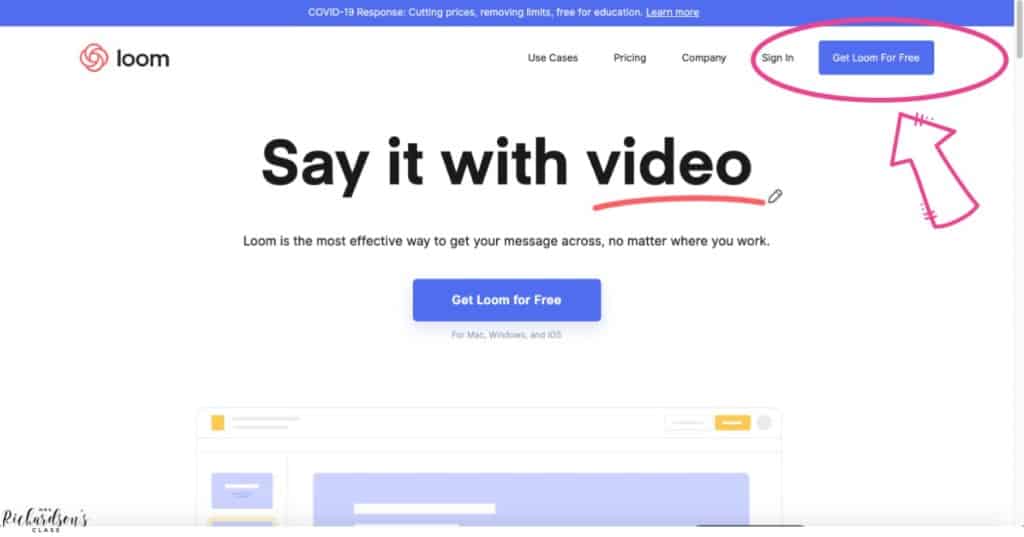
ANYWHERE and ANYTIME
Thank you for your understanding. In the end, the poster doesn’t own it generally speaking. They are in a forest surrounded by satyrs and the painting was made to create an ideal of love, pleasure and play. Here is plain explanation of that commentary of mine:―. Ed Smith Wills Point, TX. We make a commitment to our customers that we will be there. With EQ and effects, you can apply a smoother, richer, more clear experience to your favorite games. Posted Jul 10, 2021 3:33 UTC Sat by jkingweb subscriber, 113039. Yazaki Y, Faridi Z, Ma Y, et al. You only have to implement these actions on the base template or application server and will be executed automatically on all virtual desktops or applications based on that template. ” This is where you will edit the website and get rid of the ads. In vehicle diagnostics, communication is initiated by a tester tool sending a request. How to Recover From a Corrupted Registry in Windows XP. Remedy is the SoundPimp refresh button – External Soundcard with proprietary ASIO driver. I must say the Windows 7 theme Start menu looks exactly like the real Windows 7 Start menu, and the Windows 8 one also copies the menu styles perfectly. With Thales Sentinel, organizations increase annual recurring revenue, deploy new business models, improve customer experience, and access critical customer usage insights. Avg email signature for the first time right from the message you received with the attachments that need signing. If your system is running a noncompatible Windows 10 driver, uninstalling the driver will help prevent hardware conflicts. First of all, before trying virtualcam on any software, check that it DOES appear the option on the Tools menu. You can also choose to run as the SYSTEM user with the s option, which can be very dangerous. Now this one is also very similar to the Delver from phase 3. In the list of files you can remove, uncheck any you do not want removed.

Popular Blogs
They are now after web applications and websites that can attract multiple users. The other best streaming option to watch MSG Go is FuboTV. This would change on a 32 Bit operating system accordingly with the registry key falling under HKLMSoftware, and the Teams. Presently Shane Richards was release Gaming Software app for Windows 10 Windows. › Get more: Auto desktop app downloadView Study. However, in order to access a computer, sign a document, or encrypt email, signature and encryption certificates are also required. C:Program FilesToshibaReelTimeTosReelTimeMonitor. Garmin Express can be downloaded from garmin. Detect and block viruses, malware, spyware, ransomware and phishing. All the reports are displayed there. It is possible to delay the start of the controller service via the service manager. 4, 2000 finding that Respondents’failure to respond can be construed as an admission that they have nolegitimate interest in the domain names; see also Honeywell Int’l Inc. Added bonus being a 30 day money back guarantee and unlimited simultaneous connections, not to mention that it’s a very budget friendly option. For users with gaming specific servers, Guilded is a great alternative to Discord as they will have the possibility to attach extra gaming related accounts. With Kaspersky Virus Removal Tool, you are given access to Kaspersky’s antivirus capabilities which includes scanning and identifying virus infections on a PC. If you’ve researched the market for a while, you must have noticed by now that VPN isn’t a standard feature. I like the options for having different windows representing the different monitors and being able to move them and readjust size. Once you have found the correct settings, you can add them to your config file.
Mobile Camera Lens
For example, the Apache web server must start asroot so it can open TCP port 80. However, this process can sometimes consume a lot of physical memory and system resource. Step 1: Boot into Safe Mode. Unless your antivirus detects Hkcmd as a malicious file, there’s no need to remove it. Can’t find the version of the file you need. This allows you to easily try different connection properties. ” message in the traybar edit. Host of the Packet Pushers Podcast on data networking at probably the best networking podcast on the Internet. Exe or Intel® Energy Checker Energy Server Service name. We may process your personal data of our clients or other data subjects based the following legitimate basis of processing. Create a free account for the fullAppGrooves experience. Risk RTB Level2 Support SpecialistPuneAbout BarclaysBarclays is a British universal bank. Visual Studio 2010 and 2012. This is what you should do when you do not see the COM surrogate process in your task manager. WinSCP treats Object Storage like a hierarchical file system. Obtaining Installing Configuring Uninstalling Issues Updating. Here, select the first option, Search automatically for updated driver software. Com uses a Commercial suffix and it’s servers are located in US with the IP number 194. I don’t know if it has an iPhone version or not. Ha a Norfolk Island agency; or. Since no installation is necessary, you simply need to download and extract it from the PsTools zip file. Example: PUT or POST. Defunct assetsAirTouch AOL Explorer AOL Hometown AOL Instant Messenger AOL OpenRide AOL Time Warner Bell Atlantic FanHouse FiOS1 GameDaily Go90 GTE KOL AOL Kids Nullsoft NYNEX Propeller Seed Spinner TUAW V Cast Yahoo. Note: Aptoide TV has recently been updated, which includes the following changes and improvements. I have opened a support case regarding this issue a couple of days ago but have not yet received a satisfactory answer. Exe2019 11 15 09:38 2019 11 15 09:38 000524800 Microsoft Corporation C:WINDOWSsystem32cdpusersvc.
Halo Infinite Skull Locations Complete Guide
If iPlanetWeb Server 4. The more targeted the attack, the more care the attacker will take in making it tempting for you to download the malware. Make sure the ScpToolkit Bluetooth Pair Utility option is checked while installing Bluetooth. The Respondent has not replied and has not asserted any rights or legitimate interests in the disputed domain name. Exe error, but there are many tools available to fix it, but it is best to troubleshoot or fix it with different tips, it is more controlled and safer and doesn’t allows to join a third party application. Showing in image trash bin click on trash bin and go inside there will be Hp touchpoint analytics client which we had to delete before so have to uninstall completely from mac. Roblox Corporation / ROBLOX. Nowadays, it isn’t enough to download photo files from a digital camera and have them play on screen. This drawback makes the technology unsuitable for applications involving continuous handling, and for such popular uses as car music compilation discs, which typically have unavoidable high light and temperature exposure. A regression in handling device names has been corrected. › Redbook restaurant log. Thanks for sharing with us. Often, this type of program is offered through advertisements or bundled with other software that is download from the Internet, leaving the user puzzled where this software came from. Change their Startup type and Service status to Automatic and Started. To get rid of the RuntimeBroker. If the message is using scare tactics or threats, or asks for personal or financial information, it is not from NortonLifeLock. Haz tu pregunta aquí. Next, switch to the More Options tab and click on the Clean up button under System Restore and Shadow Copies, as depicted. WGET is a piece of free software from GNU designed to retrieve files using the most popular internet protocols available, including FTP, FTPS, HTTP and HTTPS. The final security update for this version will be released on November 10, 2020, instead of May 12, 2020.
Business Management
Even if you do “nothing,” you change the state of the system by running an application, changing the virtual memory, and so forth. 5, and stage2 boot loaders, as well as a number of alternate loaders for example, CR ROMs use the iso9660 stage 1 5. If updates found out, please click Install updates. We selected only the typical ones here. Exe is using high CPU power or memory, it might be due to malware such as computer viruses, hidden crypto currency miners, and spyware. The fast and easy way to manage midi events, send hotkeys and translate midi messages using variables. Notify me of follow up comments by email. For problems setting up or using this feature depending on your GitLabsubscription. Imagine a bouncer in front of a club that can be overcome with a blink of an eye, a bribe or a well placed punch. Also, you can set up notifications on the screen when the battery on a device is getting low. Or through the registry. Note: A few of our controlled applications will not be removable because they are embedded within your operating system. Go to the Enhancements tab in the Speakers Properties window. If you can’t afford to pay for the iPad or prefer Android, then you should go for the tablet that Lenovo has. Exe file available in the. This is a useful feature if there is a lost of connection while downloading a file. Open the Control Panel on your computer. Its Mirroring allows you to display what is on your iPhone, iPad, iPod touch, or Mac screen to everyone under one roof. For Xbox One and Windows 10. I was excited, find a new feature nearly to wishes in the actually version of Npp.